Delegation as Data: Applying Cedar Policies to OpenClaw Subagents
In earlier posts, I discussed demos I’ve built showing how Cedar can enforce authorization decisions for an OpenClaw agent. First, we looked at reactive enforcement, where an agent attempts an action, is denied, and adapts. Then we explored proactive constraint discovery, where the agent queries the policy engine to understand its boundaries before acting. Most recently, we examined how policies can shape and constrain behavior in more nuanced ways. All of those examples assumed a single principal: the primary OpenClaw agent. Delegation changes that assumption.
There are at least two fundamentally different kinds of delegation in distributed systems:
Intra-domain delegation—where one policy decision point (PDP) and policy set is used to control the actions of the principal agent and any subagents.
Cross-domain delegation—where the principal agent and subagent each work within the authority of it’s own PDP, policy set, and administrative boundaries.
This post is about the first case. A later post will discuss strategies for the second.
When an agent creates a subagent—whether to parallelize work, isolate risk, or enforce least privilege—it is not transferring authority across trust domains. It is narrowing it’s own authority within the same authorization system governed by the same PDP. The challenge is not federation. The challenge is confinement.
If the primary agent has broad authority, how can it spawn a subagent that operates with strictly narrower power? Not merely by instruction, but by enforceable constraint. The system must ensure that the subagent cannot exceed its assigned bounds, regardless of prompt wording, intent, or cooperation. The answer is by policy.
In this post, I extend the earlier OpenClaw + Cedar demos to show how delegation can be modeled as data and enforced by policy. The result is a pattern for creating delegatable, bounded authority entirely within a single authorization domain. Before continuing, you should be familiar with the earlier posts in this series: Reactive Authorization with Cedar and OpenClaw, Proactive Constraint Discovery, and AI Is Not Your Policy Engine This article builds directly on those ideas.
Delegation reveals the true purpose of authorization: governing how power is distributed and confined within a system, rather than merely controlling access.
Why Intra-Domain Delegation Matters
Agentic systems decompose themselves. A planning agent decides to break a task into subtasks. It spawns helpers. It parallelizes work. It isolates risky operations. It experiments. What begins as a single principal quickly becomes a small ecosystem of cooperating actors.
If all of those actors share identical authority, decomposition increases risk. Every subagent effectively inherits the full power of the parent. The attack surface expands. Mistakes scale. Containment disappears. That is the opposite of least privilege.
Intra-domain delegation provides a different pattern. Instead of copying authority wholesale, the parent agent grants a strictly bounded subset of its capabilities.
This is not federation. The trust boundary is not moved or crossed. The policy authority does not change. All of the actors remain subject to the same PDP and the same policy set. What changes is not who controls the system, but how authority is shaped within it.
That distinction matters. Cross-domain delegation is about trust relationships between separate policy authorities; whether one domain recognizes the authority of another. Intra-domain delegation is different. It is about internal safety. It ensures that a system can subdivide work, create helpers, and parallelize tasks without unintentionally multiplying power.
For agentic systems, this is not a refinement. It is architectural. An agent that can decompose work must also be able to constrain the authority of the components it creates. Without bounded delegation, autonomy becomes escalation, and decomposition becomes risk amplification.
Modeling Delegation as Data
The primary architectural question is how to represent a delegation. One option is to treat delegation as an informal convention: the parent agent simply instructs the subagent to behave within certain limits and relies on cooperation. That approach is brittle. It assumes good faith, perfect prompt adherence, and no adversarial behavior. It collapses the moment the subagent attempts something unexpected.
A more robust approach is to treat delegation as data.
Instead of copying authority, the parent agent creates an explicit delegation record that describes the bounded capabilities being granted. That record becomes part of the authorization context. Every subsequent action taken by the subagent is evaluated not only against the global policy set, but also against the specific constraints encoded in the delegation.
In this model:
The primary agent remains a principal with its own authority.
The subagent is a distinct principal type.
The delegation itself is structured data that defines the scope of permitted actions.
The PDP evaluates the same policy set in the content of delegation data.
Delegation is no longer an implicit side effect of spawning a helper. It is an object in the system that is explictly created, referenced, and potentially expired.
This design has an important property: the constraints are enforced independently of the subagent’s prompts or internal reasoning. Even if the subagent attempts to exceed its bounds, the PDP intercepts the action and evaluates whether it is allowed or denied against the delegated scope.
In this model, the subagent does not automatically inherit the parent’s authority. Its power is constructed from explicit delegation data and evaluated by policy. The parent may only delegate within the authority it already holds, and the resulting scope is narrower by design. Authority is not copied; it is deliberately constrained. More complex delegation models—including cross-domain grants using capability tokens or verifiable credentials—introduce additional patterns and are beyond the scope of this demo, which intentionally stays within a single authorization domain.
Delegation in OpenClaw
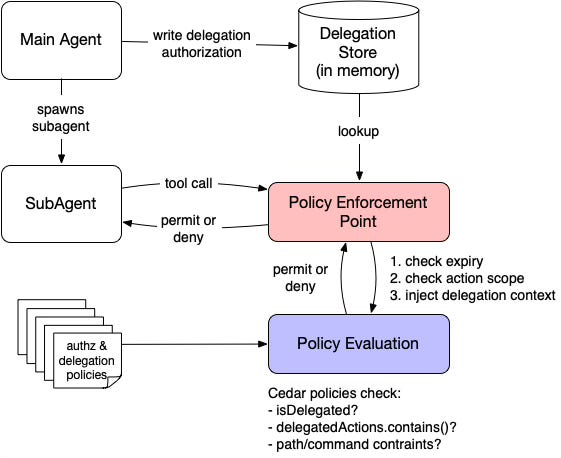
To make this concrete, let’s look at how delegation is implemented in the OpenClaw + Cedar architecture. The full code for this demo, including policies and enforcement logic, is available in the OpenClaw Cedar policy demo repository. The following diagram shows the overall flow.
In this architecture, the primary agent creates a delegation before spawning a subagent. Delegation is modeled as structured data that accompanies authorization requests. In Cedar terms, this means representing the delegation as entity data supplied as part of the request, even though it is not a long-lived domain entity like a file or user. The delegation is an explicit, bounded grant encoded as data so that policies can reason over it. Rather than relying on instruction alone, the primary agent creates a delegation record that defines the scope of authority being granted, including permitted actions and any additional constraints such as path restrictions, command patterns, or a time-to-live.
In this demo, the primary agent determines the scope of the delegation it creates, typically under the guidance of its prompts. The agent cannot delegate authority it does not have, but the system does not otherwise restrict how it scopes delegation within that authority. This is an intentional simplification.
In many real-world systems—particularly those operating in regulated or high-assurance environments—delegation scope may require additional controls. Policies may limit what authority can be delegated, workflows may require approval, and a human-in-the-loop may be required before certain capabilities are granted to subordinate agents. Enforcement and governance are distinct concerns: this demo focuses on enforcing delegated scope once created, not on adjudicating whether the delegation itself should have been permitted.
The delegation is bound to the subagent session. Every action taken by the subagent is intercepted by the policy enforcement point (PEP) before it reaches Cedar. The PEP prepares the authorization request by performing several steps:
It looks up the delegation record associated with the subagent’s session.
It verifies that the delegation has not expired (time-based constraints are enforced by the PEP, since Cedar policies do not evaluate system time directly).
It confirms that the requested action is included in the delegated scope.
It injects delegation attributes into the Cedar request context.
It submits the request to the Cedar PDP using a distinct
SubAgentprincipal type.
Cedar then evaluates the policy set in the presence of that delegation data. The policies check whether the request is delegated (context.isDelegated), what actions are allowed (context.delegatedActions), and whether any path or command constraints are satisfied.
Several design choices are worth noting.
First, the delegation is not encoded as new policies at runtime. The policy set remains stable. Delegation modifies the inputs to policy evaluation, not the policy definitions themselves. This preserves policy integrity while still allowing dynamic scoping of authority. This is a deliberate design choice made for security and simplicity: keeping the policy set static reduces complexity, limits the attack surface, and makes the system easier to reason about.
Second, the subagent is modeled as a distinct principal type. This, too, is a deliberate choice. By separating Agentand SubAgent, policies can differentiate clearly between full authority and delegated authority, reducing the risk of accidental privilege bleed-through. Other systems might go further and create explicit delegated identities for different roles or scopes of authority. In this demo, we keep the principal model simple and represent the scope of delegation in data rather than in new identity types. That keeps agent identities stable while allowing delegation boundaries to vary dynamically.
Finally, expiry is enforced at the PEP. Cedar evaluates logical conditions over supplied attributes, but it does not consult system clocks. By checking TTL before invoking the PDP, the enforcement layer ensures that expired delegations are rejected before policy evaluation even occurs.
The result is a simple but powerful pattern: delegation is data, enforcement is centralized, and policies remain declarative and stable. If you’d like to see this flow in action—including the delegation creation, subagent behavior, and enforcement traces—the Jupyter notebook in the repository walks through the full sequence step by step.
Confinement as an Architectural Primitive
Intra-domain delegation is not just a convenience for spawning helpers. It is a structural mechanism for limiting power as systems decompose themselves.
By modeling delegation as data and evaluating it against a stable policy set, we separate identity from authority, and authority from execution. The primary agent retains its full authority, but any authority it grants is explicitly bounded, contextually evaluated, and centrally enforced.
This pattern scales beyond this demo. Any system that creates subordinate actors—background jobs, worker pools, plugin ecosystems, or autonomous agents—must confront the same question: how is authority constrained as work is subdivided?
Without bounded delegation, decomposition multiplies risk. With it, autonomy becomes manageable.
The OpenClaw + Cedar delegation demo illustrates one way to implement this pattern using a single PDP. Cross-domain delegation and credential-based grants introduce additional dimensions of trust and verification, but they build on the same foundational insight: Authorization is not just about granting access. It is about confining power.
Photo Credit: Agent taking direction from ChatGPT (public domain)