Leveraging the Identity Metasystem; Technometria - Issue #34

Metasystems promote network effects because they provide leverage: one infrastructure that not only serves many purposes, but also engenders consistent behavior.
Yesterday, I noticed the following tweet (since deleted):
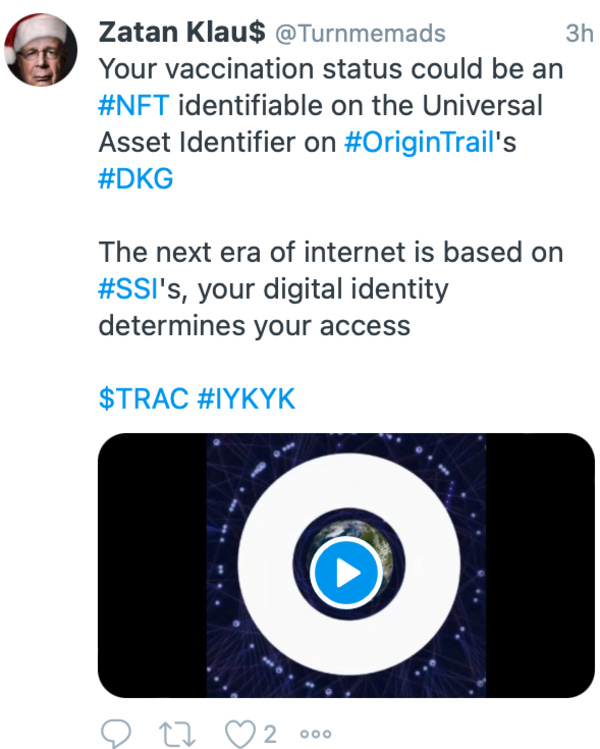
Origin Trail NFTs for SSI?
Soooo many questions:
Would a vaccination status NFT be transferable (a core feature of most NFTs)?
What’s the underlying platform’s security?
How’s the smart contract written?
Who has control?
How do identifiers work in this system?
What are the privacy implications?
How much PII is on the blockchain?
Answering these questions would require significant work. And that work might have to be redone for each NFT used for SSI, depending on how Origin Trail is architected. If they are based on ERC–721, that tells us some things we may need to know, but doesn’t answer most of the questions I pose above. If Origin Trail runs its own blockchain, then there are even more questions.
One of the big value propositions of an identity metasystem is that many of these questions can be answered once for the metasystem rather than answering them for each identity system built on top of it. In particular, the metasystem guarantees the fidelity of the credential exchange. Credential fidelity comprises four important attributes. Credential exchange on the identity metasystem:
Reveals the identifier of the issuer
Ensures the credential was issued to the party presenting it
Ensures the credential has not been tampered with
Reveals whether or not the credential has been revoked
I don’t know anything about Origin Trail. It’s possible that they have worked all this out. The point is simply that the tweet caused me to think about the advantages of a metasystem.
Metasystems give us leverage because their known behavior makes reasoning about systems built on top of them easier. Knowing how TCP works lets us know important properties of the protocols that operate on top of it. Similarly, in the identity metasystem, knowing how DIDs, DID Registries, DIDComm, and verifiable credential exchange protocols function means that we can more easily understand the behavior of a system built on top of it, like the health pass ecosystem. This leverage is an important component of the network effects that a well designed metasystem can provide.
End Notes
That’s all for this week. Thanks for reading.
Please follow me on Twitter.
If you enjoyed this, please consider sharing it with a friend or twenty. Just forward this email, or point them at my news page.
I’d love to hear what you enjoyed and what you’d like to see more (or less) of. And if you see something you think I’d enjoy, let me know. Just reply to this email.
P.S. You may be receiving this email because you signed up for my Substack. If you’re not interested, simply unsubscribe.
© 2021 Phillip J. Windley. Some rights reserved. Technometria is a trademark of PJW LC.
By Phil Windley
I build things; I write code; I void warranties
In order to unsubscribe, click here.
If you were forwarded this newsletter and you like it, you can subscribe here.
Powered by Revue

